Security isn't procedural.
It's adversarial.
Every other security approach starts from the assumption that defenders define the rules. Attackers don't follow rules. We start from where attackers start.
The compliance trap
The dominant approach to startup security is compliance-led: get a pen test, pass a SOC 2 audit, check the boxes. This approach creates the feeling of security without the reality of it.
Compliance frameworks are written by committees and updated slowly. Attackers adapt in days. By the time a new attack technique appears in a compliance checklist, it's already been used in thousands of breaches.
We don't start from frameworks. We start from the question: if a capable, motivated attacker wanted to compromise this company right now, what would they do? That question has a different answer for every startup — and it's the only question that matters.
Starting point
What does the framework require?
How would an attacker compromise this?
Scope
Defined by contract
Defined by the attacker's reality
Findings
Isolated vulnerabilities + CVSS scores
Complete attack chains with business impact
Deliverable
PDF report for the compliance file
Live briefing + remediation partnership
Outcome
Certificate of compliance
Measurably improved security posture
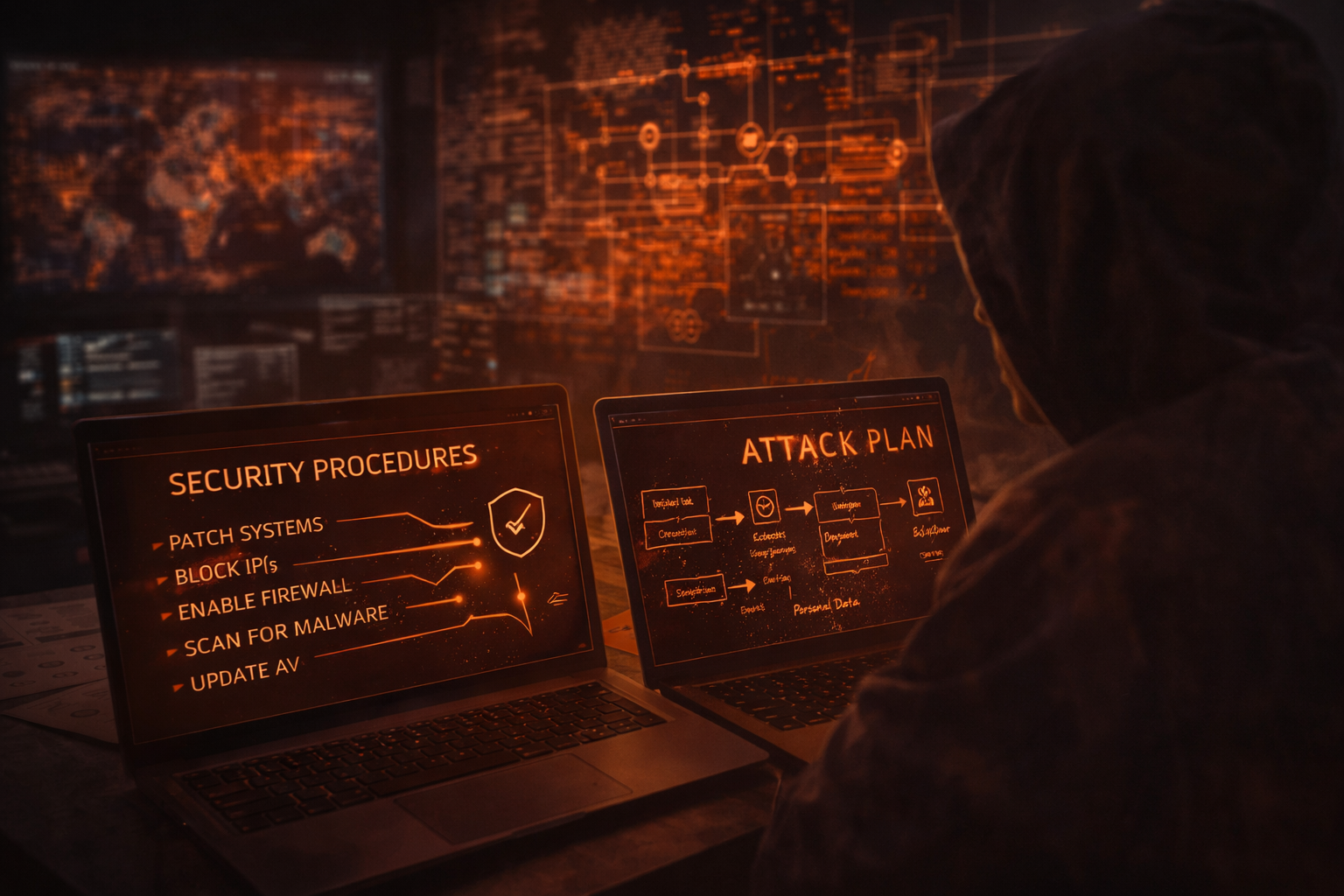
The adversarial mindset — unpacked
We think like attackers. Not because it's a clever marketing line — because it's the only model that produces accurate risk assessment.
🔍
Reconnaissance First
Before touching a system, we map everything a real attacker would know from the outside: exposed services, tech stack fingerprinting, employee information, third-party integrations.
⛓️
Chain Thinking
Real breaches chain low-severity issues together. A misconfigured S3 bucket alone is informational. Combined with a JWT weakness and an overpermissioned service role, it becomes a path to full database exfiltration.
💼
Business Impact Orientation
Every finding is evaluated against one question: what could an attacker do with this? Not "what's the CVSS score?" but "does this reach customer data?"
⏱️
Time-to-Compromise
We measure and communicate how long it would take a real attacker to achieve each impact. "This finding enables full data exfiltration within 4 hours of initial access" is more useful than any severity score.
Six principles we won't compromise on
01
Security is Adversarial
We simulate real attacker behavior. No artificial constraints. No theoretical frameworks that ignore what attackers actually do.
02
Depth Beats Breadth
We limit our client load deliberately. Three engagements done brilliantly is worth more than ten done superficially.
03
Truth Over Comfort
We deliver uncomfortable realities. Real security requires facing actual risks — not receiving a clean report that makes everyone feel better.
04
Outcomes Over Outputs
We stay engaged through remediation. We close the loop — not just the report. Improved posture, not delivered documentation.
05
Selective Partnership
We turn down more than we accept. If we can't genuinely help, we say so and refer you to someone who can.
06
Founder-Centric
You talk to us directly. The person on the discovery call is the person running the engagement. No bait and switch.
See the adversarial approach in practice.
Book a 30-minute call. We'll ask specific questions about your stack and share initial observations about your public attack surface. No template, no generic output.